Hey everyone, so today I wanted to share my walkthrough of this insider threat osint ctf from BushioToken!
So looks like we need to check out this twitter link! So lets take a look at this link and see what happens
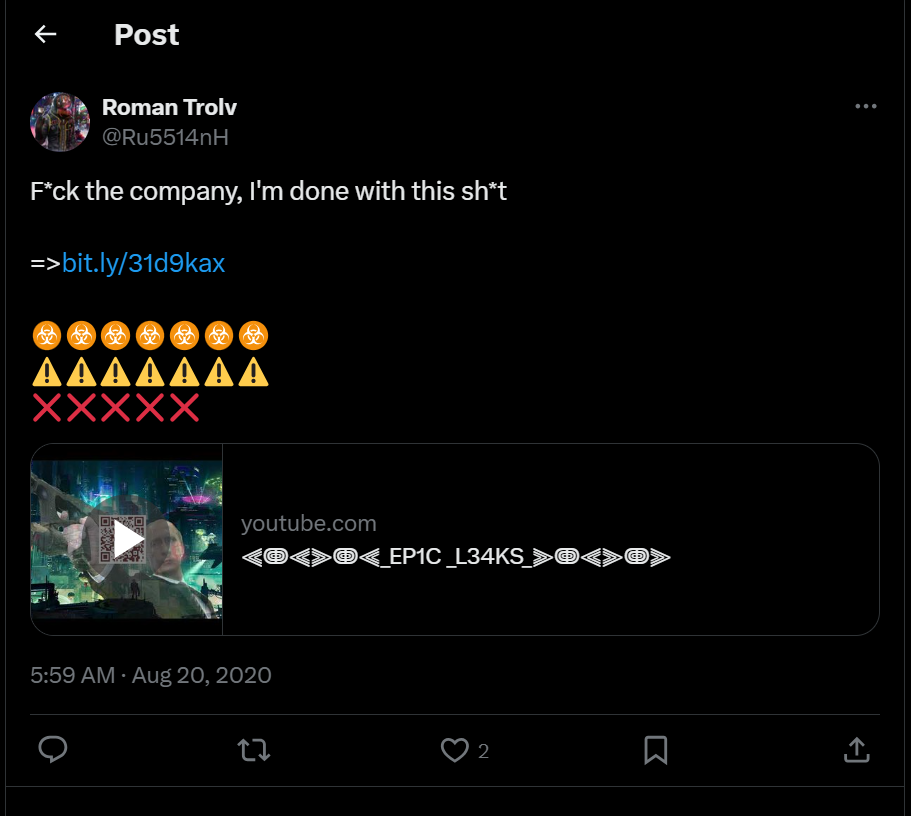
Awesome, so we see a very aggravated worker, so we can tell this person definitely is ready to do something bad. We do have some identifying information to start with
Name: Roman Trolv, now this doesn’t look like a full name maybe just abbreviated so lets dig deeper later
Userame: @Ru5514nH
so we have some interesting information so
But now we have a youtube video to look at! So first we should make sure this link is safe so so lets run it url scan

so looks like the cost is clear, lets take a look at that youtube video.
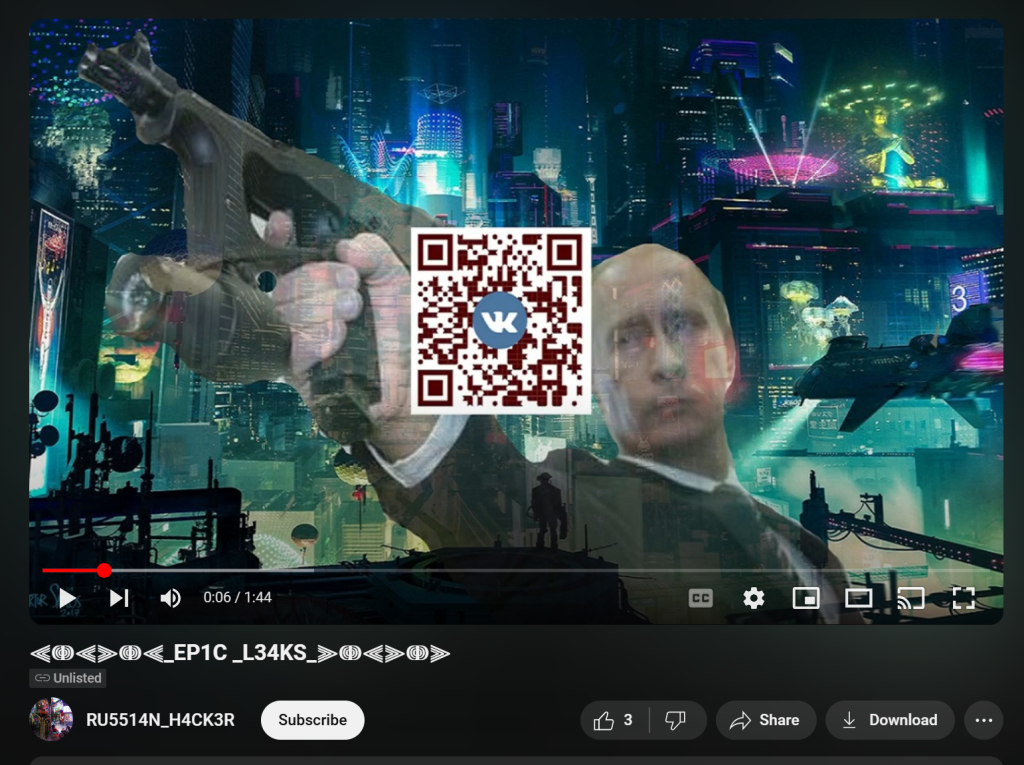
here we don’t see much we have a qr code which leads to a VK (russian social media) site and its pretty blank. Lets see if we can find any information on the youtube profile
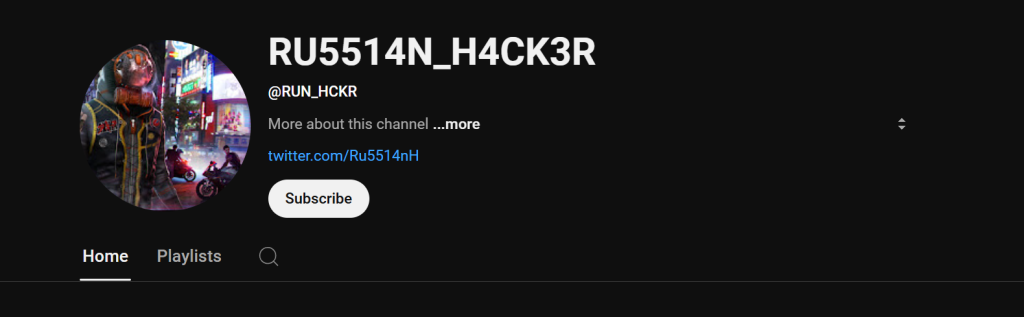
Next we see another username called @RUN_HCKR so this is interesting we now have gathered two names, so lets keep that for evidence! For now lets try and dissect that QR code.
For this one I used webQR which runs the qr code and see where it leads
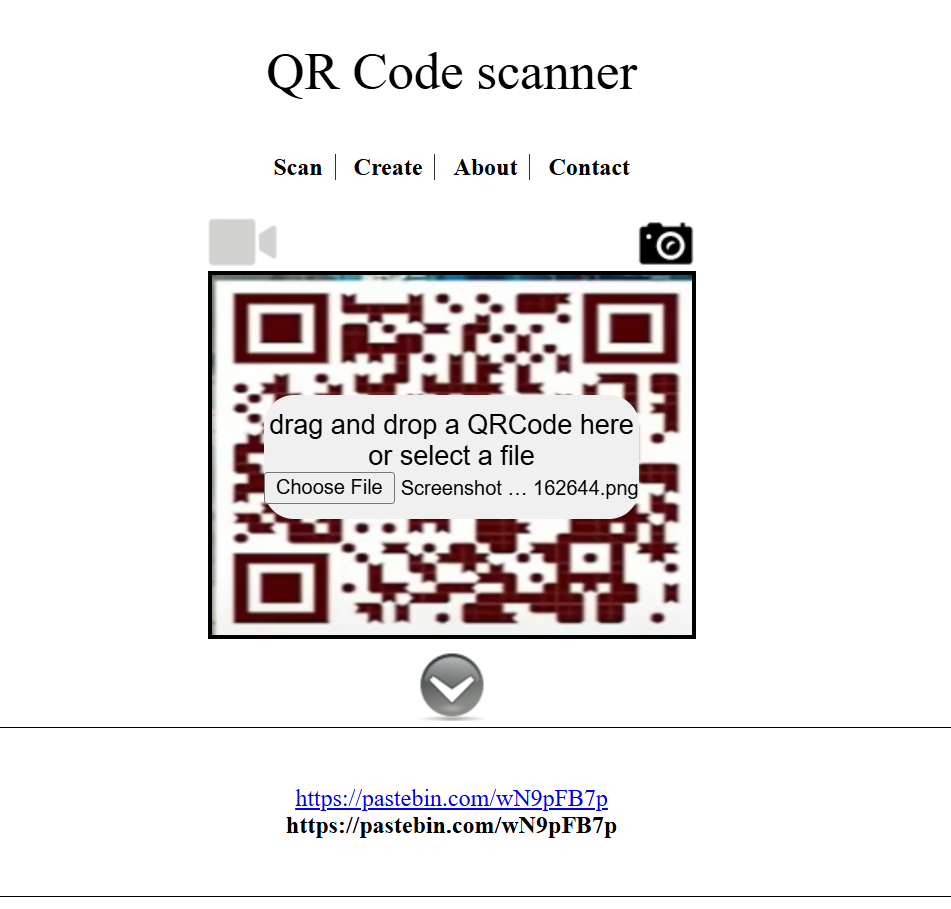
So we can see here we found a pastebin website! Seems kinda suspicious so we lets run this on our vm using tor and see where it takes us!
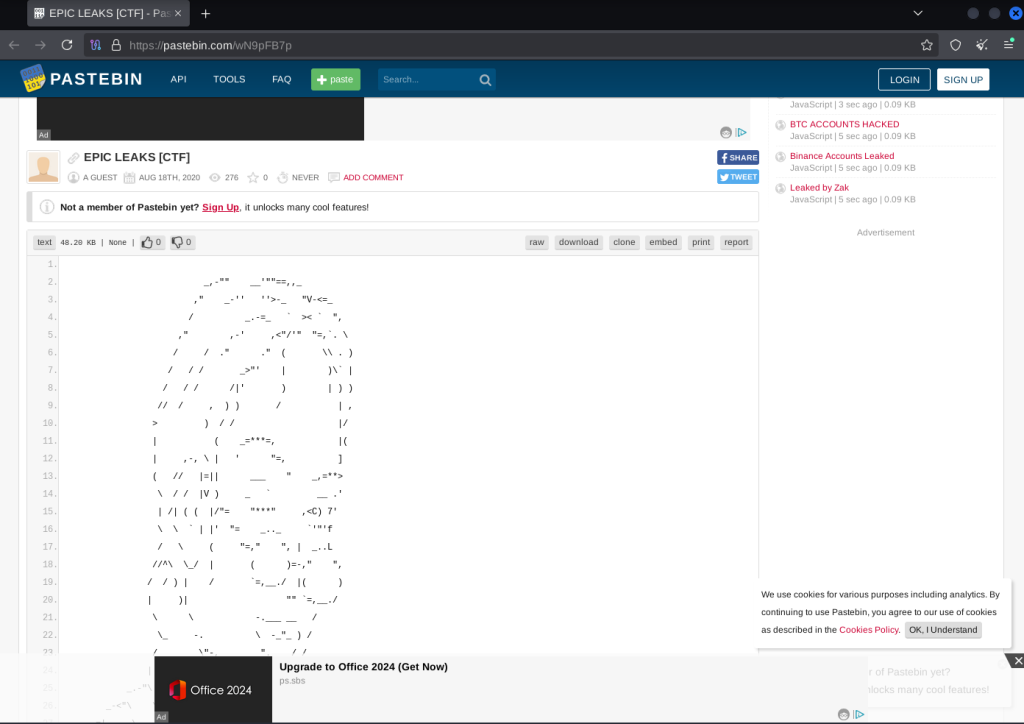
Here we can see a website and it has some pretty important information like usernames, and names. I don’t want to reveal any sensitive information because I don’t know if its fabricated. So I decided to see if I can find any clues in the website and found something good!

we can find a github! This is really huge because now we have some more personal information and this could lead to some deeper information since people tend to add a bit too much to github, so lets check it out
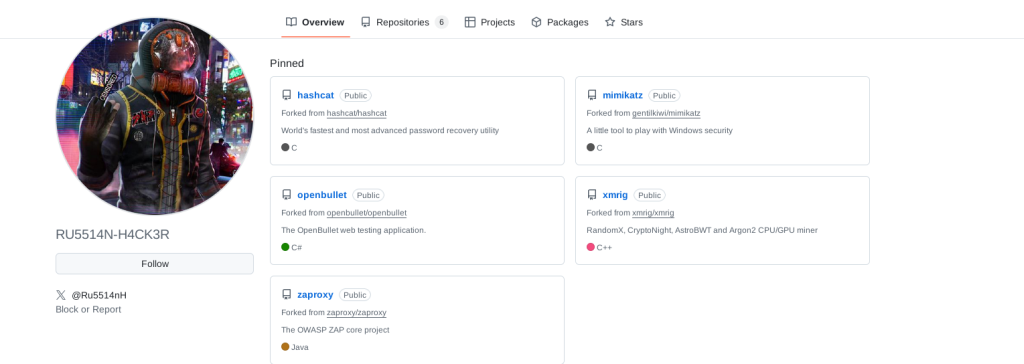
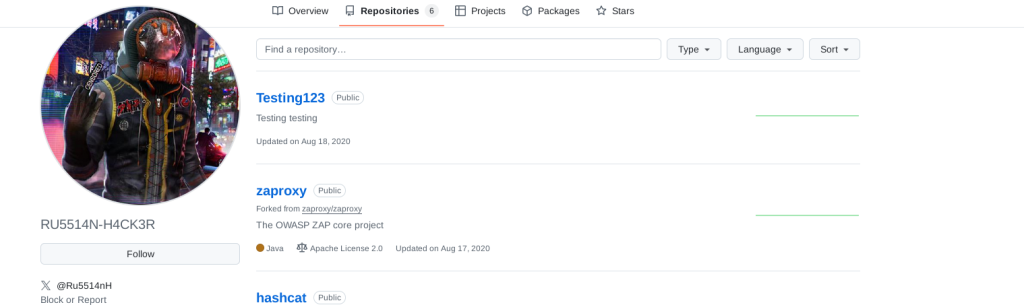
Awesome we can positively confirm that this is from the original user from Twitter from their profile picture and twitter handle! So we now have a lead. So lets see if we can find anything that can lead us to some clues
There were quite a few repo’s that looked interesting but this “testing123” stuck out to me the most so lets see whats inside
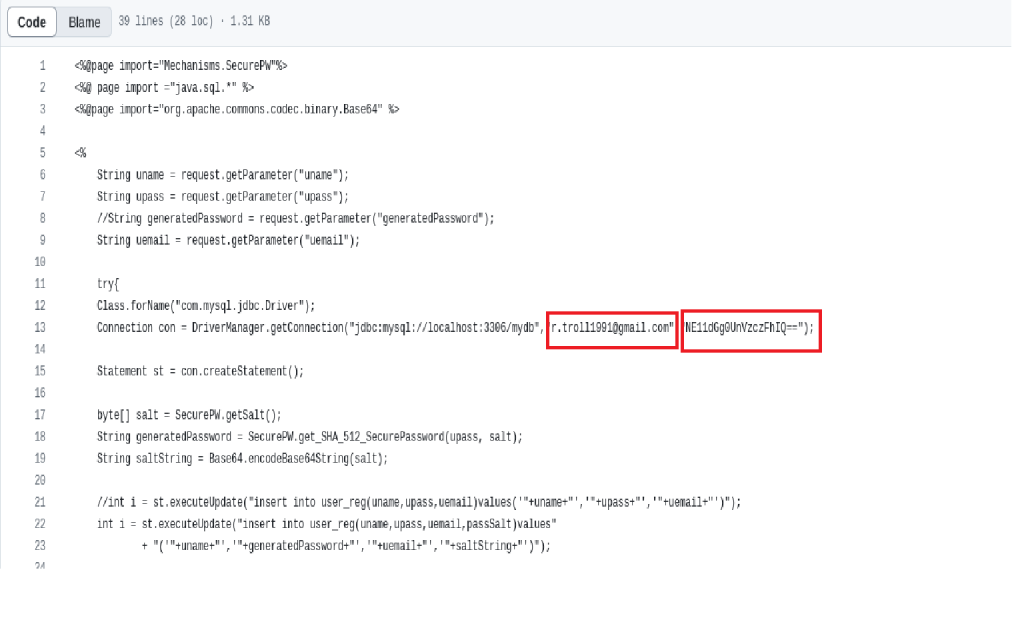
so looks like the first part of the code he added an email and a encoded password! So lets see if we can uncover that password
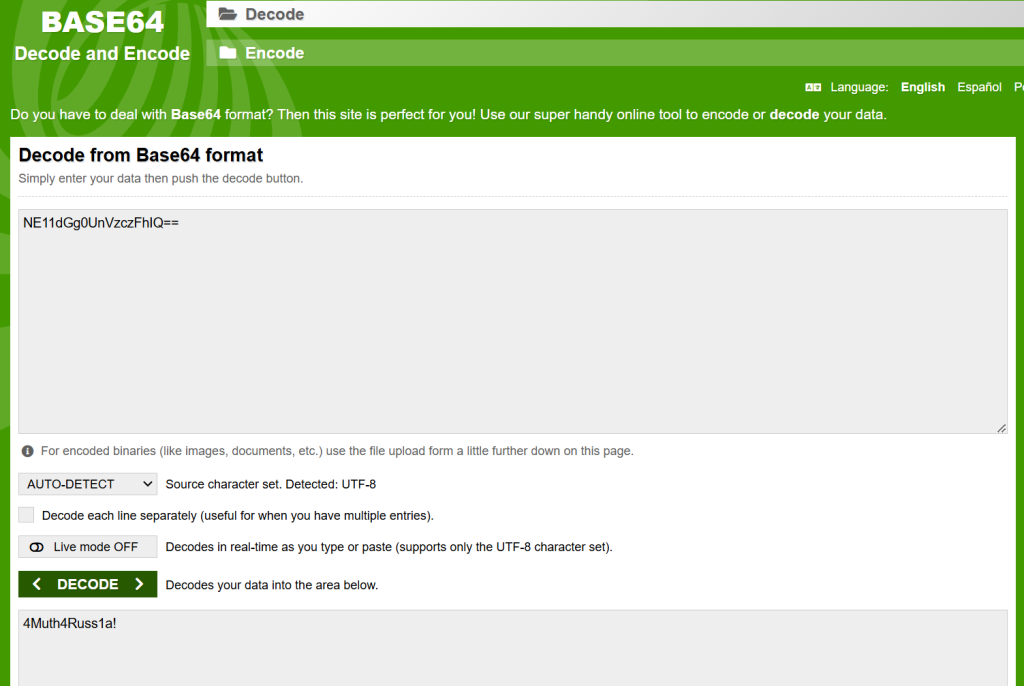
looks like we now have a password! This is a huge finding cause we have very sensitive information and could enumerate this further. BUt for now lets see if there is more information!
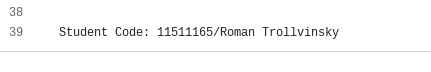
If you scroll down to the bottom of the code we do see a student code from a university class probably and a full name! So we can assume this is for a school project! This is the breakthrough we could potentially use to find this information!
So if you type in his full name in google we can find his LinkedIn!
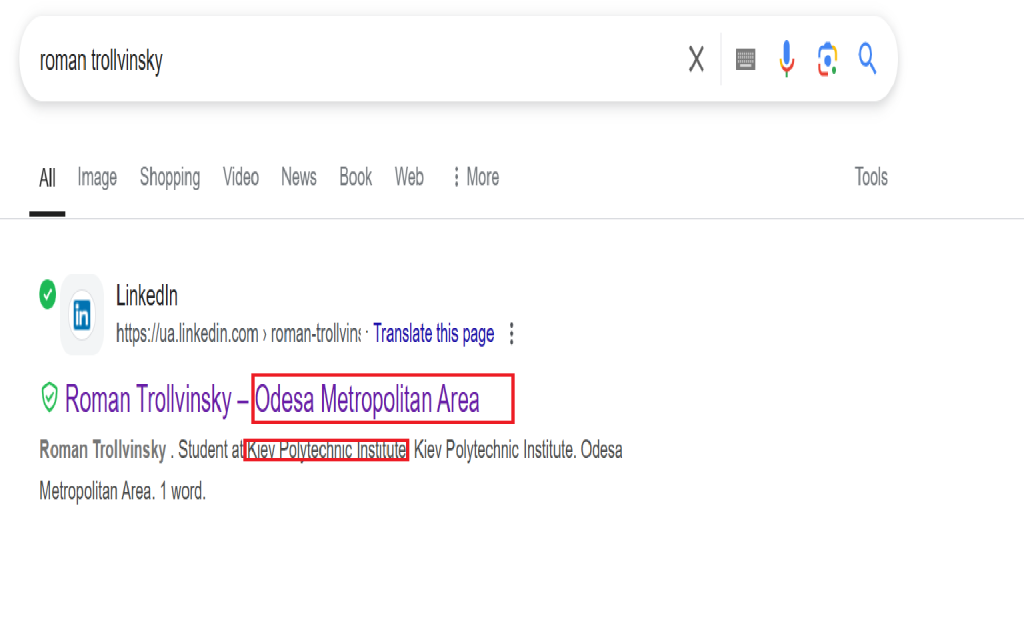
Now we did ind some key info like his name, what area he potentially lives in and what university he went to!
This is important cause this could be connected to that school project from earlier!
We dont want to necessarily want to interact with his profile incase he can see who tips him off so lets play it safe now!
Just to sweeten the deal we can look at his profile to see if he follows anyone to give us any clear information or extra leads, But his only interaction is we a football team called Shakhtar!

So if you made it this far, I wanted to say thanks for reading! So we definitely have more then enough information to give to the client so they can take legal action against the insider threat! This information is really important in corporate environments because this insider threat leaked personal information of the staff and could potentially leak proprietary data to the competitive companies. So remember there is nothing about too much information!
This concludes the Insider Threat V2 CTF by Bushido Token! If you liked it! You should definitely give it a try yourself and hope this gets your brain working on what kinda information you can find!
Take care and Happy gathering!